14 Apr How To Prevent a Cybersecurity Attack
No matter where you are on your cloud journey, it’s essential you have a cloud migration strategy to guide you. The decisions you make and the steps you take to adopt cloud services can have important implications for your business for years to come — and mistakes can be costly. That’s why it’s vital to have an experienced guide.
From building greenfield applications in the cloud to migrating databases and transforming how you do business, we can help. We can build the cloud solutions that produce the results you want. We’ll show you which applications are suitable for the public cloud, and which might require dedicated infrastructure. And we can help ease the burden of managing and securing it.
Thousands of customers around the world rely on us every day for help managing their workloads across dedicated hosting environments, AWS, Microsoft®, Google Cloud Platform™, VMware®, and OpenStack®. Let us help you migrate to an agile, highly-available, secure solution that will continue to work for you as your business grows and changes.
******************************************************************************
Is Preventing a Cybersecurity Attack One of Your New Year’s Resolutions?
2023 could be considered a highly successful year from the perspective of both security professionals and cybercriminals. Security teams leveraged groundbreaking technologies to successfully fend off attacks that would have devastated their organizations in years past. At the same time, we saw the rise of new cyber threats that targeted organizations of all sizes and led to serious financial consequences for many.
As cybersecurity enters a new era of automated breach prevention, not just breach detection, security companies may begin to achieve even greater victories in the cyber arms race. But it’s ultimately up to the businesses at the center of the fight to ensure they’re armed for battle.
Are you armed for battle?
Contact us to learn about how we can help you prevent a cybersecurity attack.
******************************************************************************
Enhance Security in a Multi-cloud World
Now’s the time to adjust your security strategy — don’t wait before your perimeter defenses are no longer effective against cyberattacks. Beyond prevention, you need swift breach detection and remediation to minimize the time criminals spend in your environment and the harm they can cause.
Breach Detection
Actively searching for threats is important for keeping your business safe. To find threats, you need a team that monitors and manages your environment 24x7x365, using advanced technology and analytics.
Minimizing Breach Window
The most precious resource for a threat is time. So your security strategy must include an approach to closing the breach window as quickly as possible — the longer you are in a vulnerable state, the more damage you are susceptible to.
Threat Remediation
Managed service providers within our portfolio not only notify you of a breach, but act on anomalous events immediately, on your behalf, based on pre-approved actions.
Reducing TCO
By turning to a Managed Service Provider with the resources and experience to detect and respond to security events on your behalf, you can help ensure your environment’s security while reducing your TCO.
******************************************************************************
Banking Industry
We are here to help regional banks with their journey to the cloud.
We understand your concerns about control, security, and compliance. Every day, we work with financial institutions of all sizes to design solutions that address their business and regulatory needs, while leveraging the power of the cloud for a competitive edge.
Whether your firm specializes in investments, banking, accounting or other financial services, you can rely on our experts with proven industry experience. We’ve already helped some of your colleagues and competitors:
- Secure their infrastructure
- Protect their data and applications
- Maintain compliance while embracing the agility of the cloud
After you’ve made a move, we’ll continue to provide ongoing guidance and operational support — so you can focus on delivering financial services to your customers.
In SOS Support, we offer the following solutions:
- Fully Managed Hosting
- Secure, Private Cloud
- Encrypted Storage
- Managed Public Cloud
- Managed Security Services
- Privacy and Data Protection
******************************************************************************
WHAT IS THE COST OF IT SECURITY BREACHES?
The costs associated with security breaches are going up, jumping 29 percent since 2013 to more than $4 million per incident in 2016, according to Ponemon’s annual benchmarking report. In addition, when it comes to the impacts of breaches – such as cost per record lost – Ponemon says the gap is widening between organizations that are unprepared and those that have added policies and processes like incident response plans, encryption, and employee training.
To calculate the average cost of a data breach, Ponemon collects both the direct and indirect expenses as well as opportunity costs incurred by the organization as follows:
-
Direct cost –
the direct expense outlay to accomplish a given activity, such as engaging forensic experts, outsourcing hotline support and providing free credit monitoring subscriptions and discounts for future products and services.
-
Indirect cost –
the amount of time, effort, and other organizational resources spent in the aftermath of a breach, such as in-house investigations and communications. This category also includes the extrapolated value of customer loss resulting from turnover.
-
Opportunity cost –
the cost of lost business opportunities resulting from negative reputation effects after the breach has been reported to victims and publicly revealed to the media.
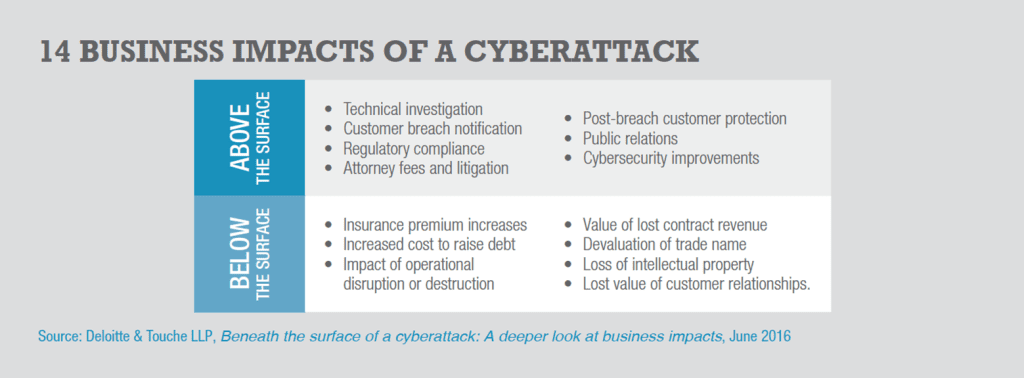
A 2016 report from Deloitte Advisory says the costs of a cybersecurity breach could be higher than most data show as the costs can rack up for many years after the initial incident. The firm identified 14 cyberattack impact factors, including seven that are hiding beneath the surface and account for 95 percent of the financial impact. (see chart, “14 Business Impacts of a Cyberattack”).